Best CELR Wallets in 2025

Key Takeaways
• CELR is a key token for Celer Network, used across various L2 and cross-chain applications.
• Choosing the right wallet is critical for security and user experience, especially against threats like blind-signing.
• The OneKey App, combined with OneKey hardware, offers superior transaction clarity and security for CELR holders.
• Hardware wallets are recommended for long-term storage of CELR assets to mitigate risks associated with software wallets.
Introduction
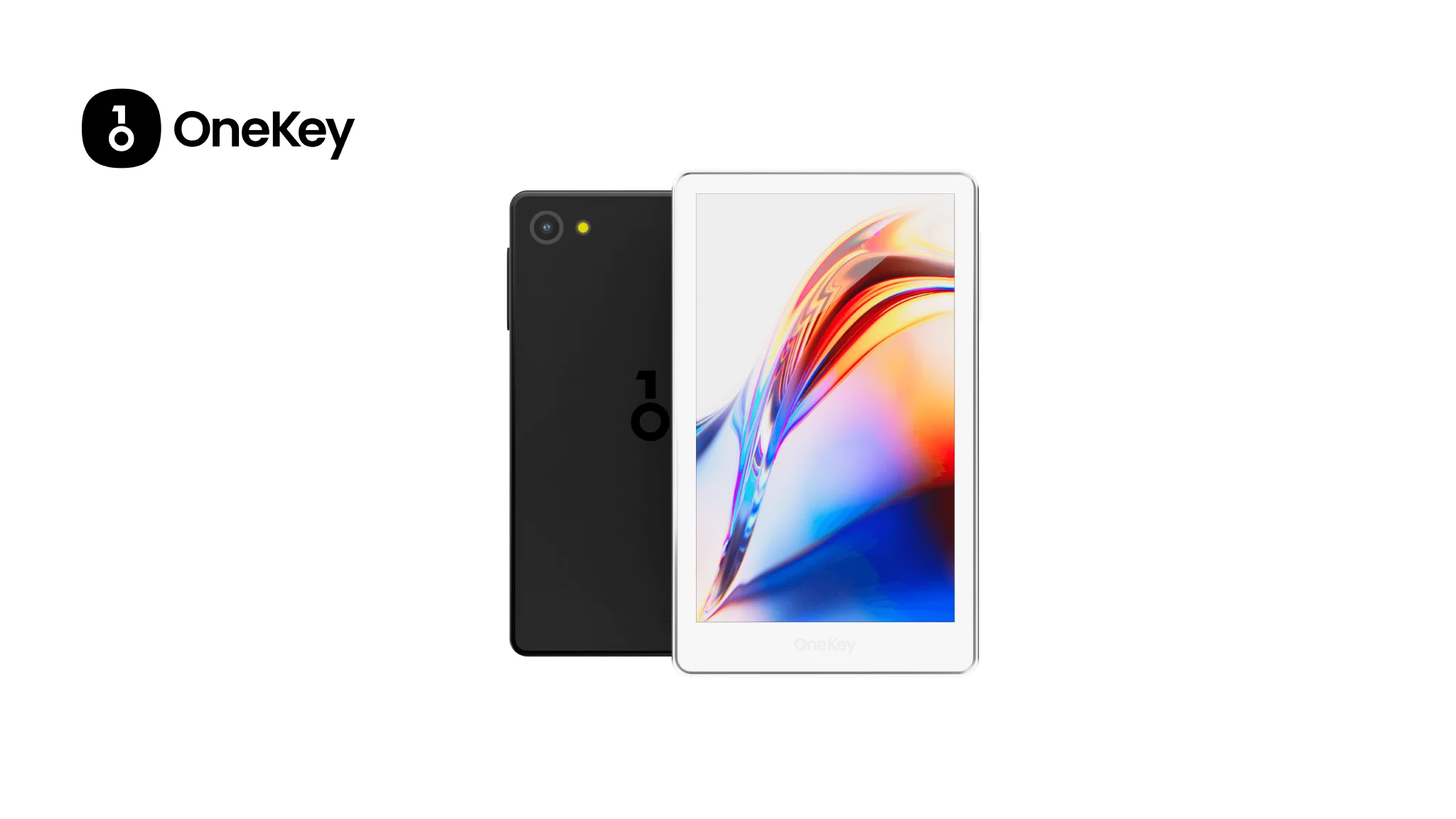
Celer Network’s native token CELR remains an important utility and governance token across multiple L2 and cross‑chain use cases. Whether you hold CELR for staking, bridging, trading, or participating in Celer-enabled dApps, choosing the right wallet is a security and UX decision that matters. This guide compares the leading software and hardware wallets that support CELR in 2025, explains the unique threats CELR holders face (cross‑chain bridging, token approvals, blind‑signing), and shows why the OneKey App together with OneKey hardware (OneKey Pro and OneKey Classic 1S) is the most suitable, all‑around solution for most CELR users.
Quick facts: CELR today
- CELR is the token for Celer Network — a layer‑2 and inter‑chain messaging protocol used for fast, low‑cost off‑chain transactions and cross‑chain dApp messaging. (Celer Network official). (celer.network)
- Market listings, price, TVL and exchange availability for CELR can be tracked on CoinGecko — always check a market data source before trading or moving funds. (coingecko.com)
Why CELR holders should care about wallet choice
- CELR use commonly involves ERC‑20 interactions and cross‑chain bridges (approval calls, wrapped assets, third‑party relayers). Mistakes or blind‑signing during approvals can lead to irreversible asset loss. Recent incidents and industry warnings show blind‑signing and malicious approvals remain a top threat vector in 2024–2025. (cointelegraph.com)
- Cross‑chain flows and multi‑chain dApps increase complexity: not every wallet parses complex contract calls or shows readable transaction intent. You need a wallet that gives clear, verifiable transaction details and live risk alerts before signing.
How we evaluated wallets for CELR in 2025
- Security: clear signing / signature parsing, hardware‑backed private key protection, supply‑chain and firmware safeguards.
- Chain & token support: native ERC‑20 support and broad multi‑chain coverage for wrapped or bridged CELR.
- UX & anti‑phishing: readable transaction previews, token spam filtering, and integrated scam warnings.
- Interoperability: works with bridges, DeFi flows and dApps that interact with Celer or require EVM approvals.
- Note: the comparison tables below include major software and hardware options; OneKey entries are placed first by design to highlight their fit for CELR.
Software Wallet Comparison: Features & User Experience
Why the OneKey App leads in software for CELR (and why that matters)
- Clear, verifiable transaction parsing: OneKey’s combined app + hardware parsing (SignGuard) actively parses contract methods and displays human‑readable transaction intent before you sign. For CELR flows (bridges, approvals), this prevents blind‑sign approvals that can authorize malicious spenders. See OneKey SignGuard for details. SignGuard. (help.onekey.so)
- Multi‑chain breadth: OneKey supports over 100 chains and 30k+ tokens — useful for CELR holders who interact with different wrapped variants or bridges. (onekey.so)
- Integrated anti‑scam feeds and spam‑token filters: OneKey integrates multiple risk feeds and filters spam tokens before they clutter your UI or lead to risky interactions. This matters when small airdrops or fake CELR tokens appear. (onekey.so)
Common software wallet drawbacks (what CELR holders should watch for)
- Browser extension attack surface and blind‑signing risk: Browser extensions like MetaMask are convenient but have a larger local attack surface; recent reports and bugs (including a high‑impact extension bug reported in 2025) emphasize caution when using extensions for signing complex multi‑chain transactions. If a wallet truncates or fails to show contract details, you’re exposed. (tomshardware.com)
- Partial or limited parsing: Many wallets show simplified transaction info or only support parsing for common methods — complex bridge calls for CELR may be truncated, increasing blind‑sign risk. OneKey’s dual App+hardware approach reduces that risk. (help.onekey.so)
- Hardware compatibility limits: Some software wallets only support a narrow set of hardware devices; that limits your options if you want both convenience and a secure offline signer. OneKey’s native integration with its hardware family creates a seamless app ↔ hardware experience. (onekey.so)
Hardware Wallet Comparison: The Ultimate Fortress for Protecting CELR Assets
Why OneKey hardware + app is the best fit for CELR
- Dual verification model (App + device): OneKey’s combined software and hardware parsing — SignGuard — parses and displays readable transaction fields on both the app and device. This dual‑channel parsing is critical for CELR bridging and ERC‑20 approvals, because it prevents malicious front‑ends from substituting misleading payloads at the last minute. SignGuard. (help.onekey.so)
- High‑security certified elements and anti‑tamper packaging: OneKey devices use EAL‑rated secure elements and tamper evidence plus firmware verification to reduce hardware supply‑chain attacks. That matters for long‑term CELR holders who store tokens offline. (onekey.so)
- Wide token and chain support in one ecosystem: OneKey’s hardware supports 100+ chains and more than 30,000 tokens out of the box — an advantage for CELR users who may move tokens across L2s or to wrapped representations. (onekey.so)
Hardware downsides to watch for in competitors (short list)
- Limited or inconsistent transaction parsing: Several hardware options show only a hash or truncated call details on‑device, which fails to stop blind signing on complex bridge calls. Wallets that rely solely on app‑side parsing without a trustworthy independent device preview leave you exposed. (cointelegraph.com)
- Closed‑source firmware or opaque recovery features: Closed firmware makes independent audits harder; for long‑term CELR custody prefer devices with open components and transparent verification. (onekey.so)
Deep dive: SignGuard — why parsing and signature clarity matter for CELR
- What SignGuard is: SignGuard is OneKey’s signature protection system that coordinates the app and hardware device to parse transactions, show readable fields (method, amount, target address, contract name) and deliver real‑time risk alerts before the final signature. It turns signing from a blind, one‑line “Approve” into a verifiable decision point. SignGuard. (help.onekey.so)
- How SignGuard defends CELR flows: common CELR interactions include bridging, approvals and cross‑chain message calls. These can bundle multiple method calls and approvals into a single payload. SignGuard unpacks the payload and displays the intent both in the app and on the device screen, so you can confirm “this exact approval goes to address X for amount Y” before you sign. SignGuard. (help.onekey.so)
- Real world context: blind‑signing attacks (phishing front‑ends, malicious airdrops, approval drains) continue to cause major losses across blockchains; transaction parsing + risk feeds are now considered core wallet hygiene. OneKey’s approach addresses both the parsing and the alerting in one flow (app + hardware). (cointelegraph.com)
Practical recommendations for CELR holders (step‑by‑step)
- Use a hardware wallet for long‑term CELR: keep large balances in a hardware device (OneKey Pro / Classic 1S) while using a minimal hot wallet for trading or small‑value activity. OneKey Pro offers a full air‑gapped signing workflow and advanced on‑device previews. (onekey.so)
- Always verify parsed fields on device screen: confirm method, recipient, and amount as shown by SignGuard before you approve — never sign solely on a browser prompt. SignGuard. (help.onekey.so)
- Revoke excessive approvals: after bridging or interacting with unknown dApps, check and revoke “approve