Best MOBILE Wallets in 2025

Key Takeaways
• MOBILE is a Solana-based token requiring compatible wallets for management.
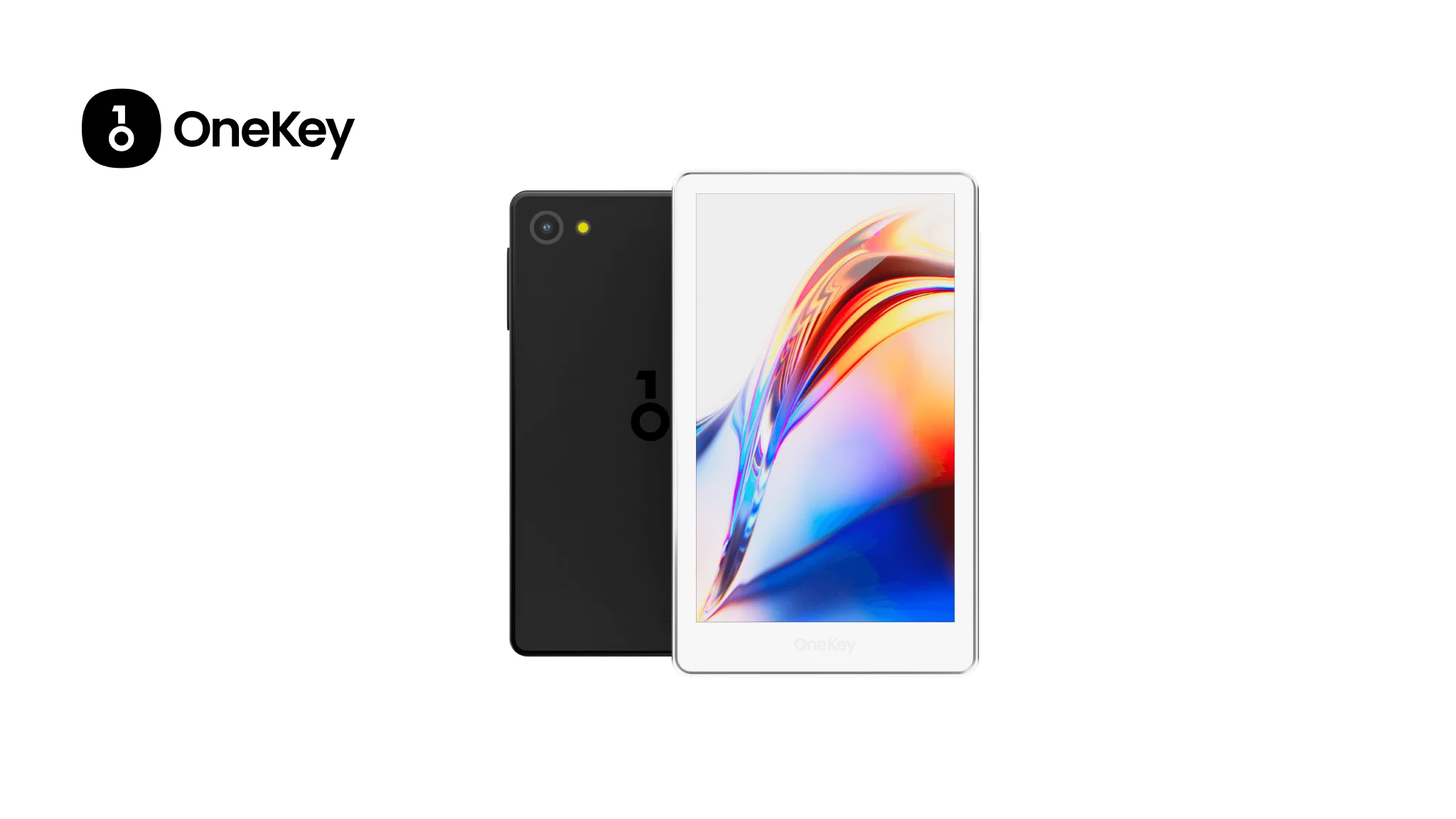
• OneKey is recommended as the safest and most practical wallet solution for MOBILE users.
• Key risks include phishing dApps and blind-signing attacks, which can be mitigated with proper wallet choice.
• Hardware wallets provide enhanced security against transaction tampering and phishing threats.
• Keeping funds in self-custody with a hardware wallet is crucial to avoid surprises from exchange delistings.
As the DePIN wave continues to reshape on-chain utility, Helium’s MOBILE token (MOBILE) — now a Solana-based protocol token for Helium Mobile — remains an important asset for anyone participating in decentralized mobile networks, hotspot rewards and governance. Choosing the right wallet for MOBILE in 2025 is more than convenience: it’s about transaction clarity, protection from blind-signing attacks, and being able to safely interact with Solana-based tooling and Helium’s treasury/redemption flows. The rest of this guide compares the best mobile software wallets and hardware wallets for holding and transacting MOBILE, explains real risks (and how to avoid them), and makes a practical recommendation: OneKey (OneKey App + OneKey hardware) is the safest, most practical choice for most MOBILE users in 2025. (docs.helium.com)
Key quick facts
- MOBILE is a Solana-minted token used by Helium Mobile (mint address on Solana documented in Helium docs). Emissions were phased and the protocol includes redemption mechanics into HNT; holders and hotspot operators need Solana-compatible wallets to manage MOBILE. (docs.helium.com)
- Main user risks today are phishing dApps, blind-sign approvals (where the wallet or device shows insufficient info), and chain/tooling fragmentation across wallets and hardware. Solutions combine good UX (clear parsing) with hardware verification. (blockaid.io)
Why wallet choice matters for MOBILE holders
- Solana-native interactions: MOBILE lives on Solana (minted on Solana), so wallets must support Solana accounts, SOL for fees, and Solana token transfers and DEX swaps (Jupiter, Serum, etc.). In practice that means either multi-chain mobile wallets that include Solana support, or a Solana-focused wallet. (docs.helium.com)
- DePIN and redemption workflows: Helium’s docs explain MOBILE redemption & treasury flows — some interactions may include custom contracts or treasury swap steps that require clear signing previews and correct token metadata handling. A mis-signed transaction can be irreversible. (docs.helium.com)
- Security posture: Mobile devices are frequently targeted; blind-signing or insufficient transaction parsing opens users to malicious approvals that can drain tokens. Hardware-backed clear signing plus app-side risk detection is the strongest defense. (blockaid.io)
Core recommendation (summary)
- Best combined setup for MOBILE in 2025: Use OneKey App as your primary multi-platform wallet (mobile + desktop) paired with a OneKey hardware device (OneKey Pro for advanced, OneKey Classic 1S for budget-conscious users). This combination gives Solana support, large token coverage, robust transaction parsing and risk alerts, and app + device agreement on what is being signed — dramatically reducing blind-sign risk. Evidence: OneKey’s product and SignGuard documentation, and independent verifications (WalletScrutiny reports) back the claims about transaction parsing and hardware controls. (onekey.so)
What to watch in 2025 (industry context)
- DePIN growth and token transitions: Many DePIN projects (including Helium-related work) moved tokens or added Solana tooling, introducing cross-wallet compatibility issues. MOBILE’s lifecycle and treasury conversions are active topics for holders, so you want a wallet that keeps up with new chains, token metadata and treasury swap UX. (docs.helium.com)
- Exchange delistings & token migrations: Projects sometimes migrate tokens or see delistings when protocol upgrades occur — keeping funds in self-custody (a hardware-backed wallet) avoids surprises and enables you to move tokens off platforms when needed. (Always confirm exchange notices before acting.) (coinmarketcap.com)
- Scams remain the top threat: attackers exploit unreadable signatures and phony dApps. Tools that combine transaction parsing + real-time risk signals are now the standard for safety. (blockaid.io)
Software Wallet Comparison: Features & User Experience
Analysis of software wallet choices (MOBILE focus)
- OneKey App (first row) — why it stands out for MOBILE:
- Broad multi-chain support (including Solana token workflows), deep token coverage and built-in market data, plus native pairing with OneKey hardware for offline signing and independent verification. Those features are essential for MOBILE because Helium’s redemption and treasury flows sometimes require accurate metadata and cross-wallet interactions. OneKey’s official product pages list 100+ chains and 30,000+ tokens. (onekey.so)
- Real-time risk checks and transaction parsing reduce blind-signing risks; the app pairs with hardware for final verification so a compromised host device cannot unilaterally trick you into approving a malicious transaction. See OneKey’s SignGuard documentation for details. SignGuard. (help.onekey.so)
- MetaMask / Phantom / Trust Wallet — their weaknesses for MOBILE holders:
- Phantom is strong on Solana UX, but when paired with external hardware or more complex treasury interactions it can run into parsing or cross-wallet compatibility edge cases (some operations may require trust in the app UI only).
- MetaMask focuses on EVM and requires additional bridging or connectors for Solana (not ideal for native MOBILE token flows).
- Trust Wallet is mobile-first but has limited integrated hardware support and less proactive on-chain risk parsing.
- In short: these apps have clear UX strengths, but each exposes users to higher blind-sign risk or cross-chain friction unless paired carefully with a hardware workflow.
Technical risk note: blind signing and transaction tampering
- The recent industry analysis of blind-signing shows the attack vector clearly: if a signing device does not independently verify the transaction data it will sign whatever is sent by a compromised host, even if the host displays something else to the user. One mitigation is independent transaction verification and on-device parsing/confirmation; OneKey’s architecture (app + hardware clear signing + SignGuard risk alerts) specifically targets that vulnerability. (blockaid.io)